Core Finding
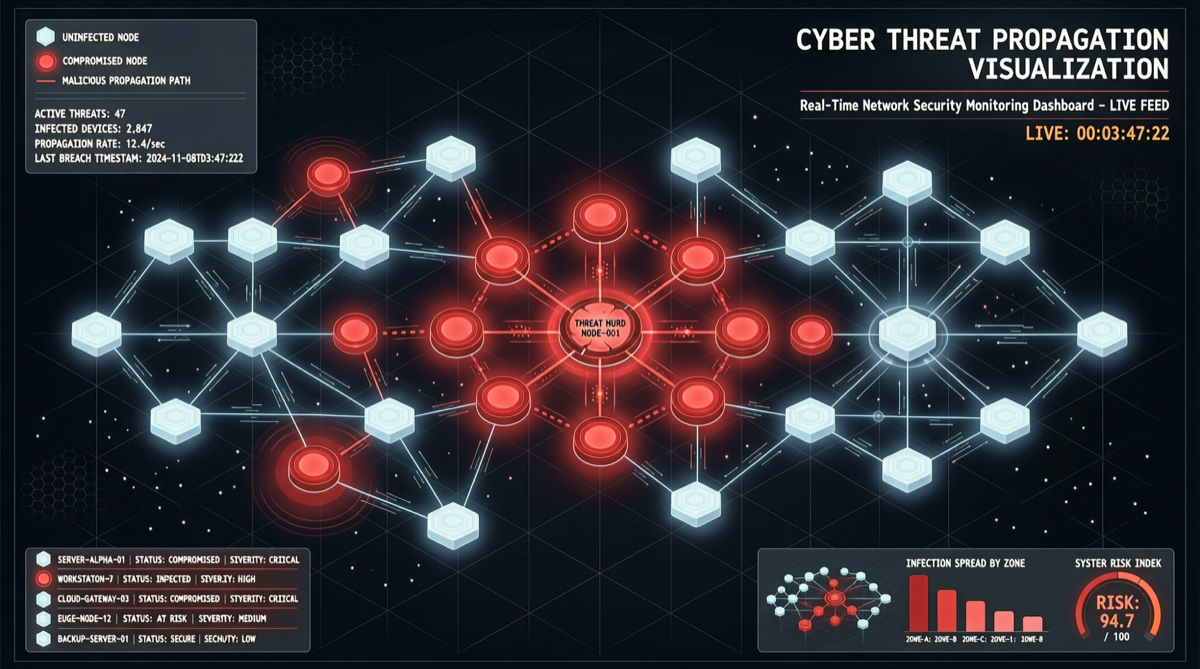
Microsoft’s security research team disclosed a novel attack vector for multi-agent systems this week: a single malicious message can propagate hop-by-hop across multi-agent networks.
The process:
- Attacker sends a carefully crafted malicious message to Agent A
- Agent A, processing the message, is induced to produce an output containing hidden instructions
- Agent B takes Agent A’s output as input, unknowingly inheriting the hidden instructions
- Agent B executes the hidden instructions, extracts private data, and produces a new malicious output
- Agent C receives Agent B’s output… the infection chain continues
Key insight: This is not about one agent being compromised. The entire agent network can be gradually infected by a single message.
Why This Problem Was Only Discovered Now
Multi-agent systems are one of the hottest directions in the AI industry in 2026:
- Anthropic’s Claude Cowork is building multi-agent collaboration workflows
- OpenAI’s Codex Workflow Engine supports multi-agent orchestration
- Open-source frameworks like Hermes Agent, CrewAI, and LangGraph are all pushing multi-agent architectures
- Enterprises are deploying dozens or even hundreds of agents for complex business processes
The industry ran ahead of security. While everyone is busy making agents more powerful, more autonomous, and better at collaboration, few stopped to ask: what happens if one agent gets infected?
Microsoft’s research gave the answer: the entire network gets infected.
Defense Recommendations
For Multi-Agent System Designers
- Implement input validation layers: Each agent’s output should be independently validated before entering the next agent
- Establish trust boundaries: Agents at different security levels should run in isolated environments
- Audit inter-agent communication: Record all message passing between agents for post-incident tracing
- Limit agent permissions: Each agent should only have the minimum permissions needed for its task
For Enterprise Agent Deployers
- Map your agent topology: Understand each node’s role and connections in your agent network
- Identify critical paths: Find agents whose infection would affect the entire network
- Deploy anomaly detection: Monitor agent behavior patterns for abnormal outputs or operations
- Prepare incident response plans: How to quickly isolate and recover when an agent is infected
Summary
Microsoft’s multi-agent cross-infection research and UC Santa Cruz’s agent poisoning paper together point to the same conclusion: the more capable AI agents become, the greater their security risk; when multiple agents collaborate, the risk is not linearly additive but exponentially amplified.
This is not about stopping multi-agent development — it is about building security in from day one.