Bottom Line First
CyberSentry is a newly open-sourced autonomous cybersecurity agent project that combines large model reasoning capabilities with a real security toolchain. This isn’t the “AI generates a penetration testing report” gimmick — it actually makes the AI work like a security engineer: analyze the target → select tools → execute → interpret results → adjust strategy.
Where the Pain Points Are
Traditional security testing faces two core problems:
- Tool fragmentation: Nmap, Nikto, SSLyze, Gobuster — each tool has its own syntax and output format, and security engineers need to manually chain them together
- High experience threshold: When should you run Nmap? What’s the next step after discovering an open port? These judgments require extensive hands-on experience
CyberSentry’s design philosophy uses an LLM as the decision-making hub, chaining tool execution into an automated workflow.
Technical Architecture
| Component | Description |
|---|---|
| Inference Engine | Llama 3.1 70B (NVIDIA NIM) |
| Reasoning Mode | ReAct (Reasoning + Acting) |
| Integrated Tools | Nmap, directory fuzzing, SSL checker, CORS detection, Cookies analysis, Headers inspection, and more — 8 total |
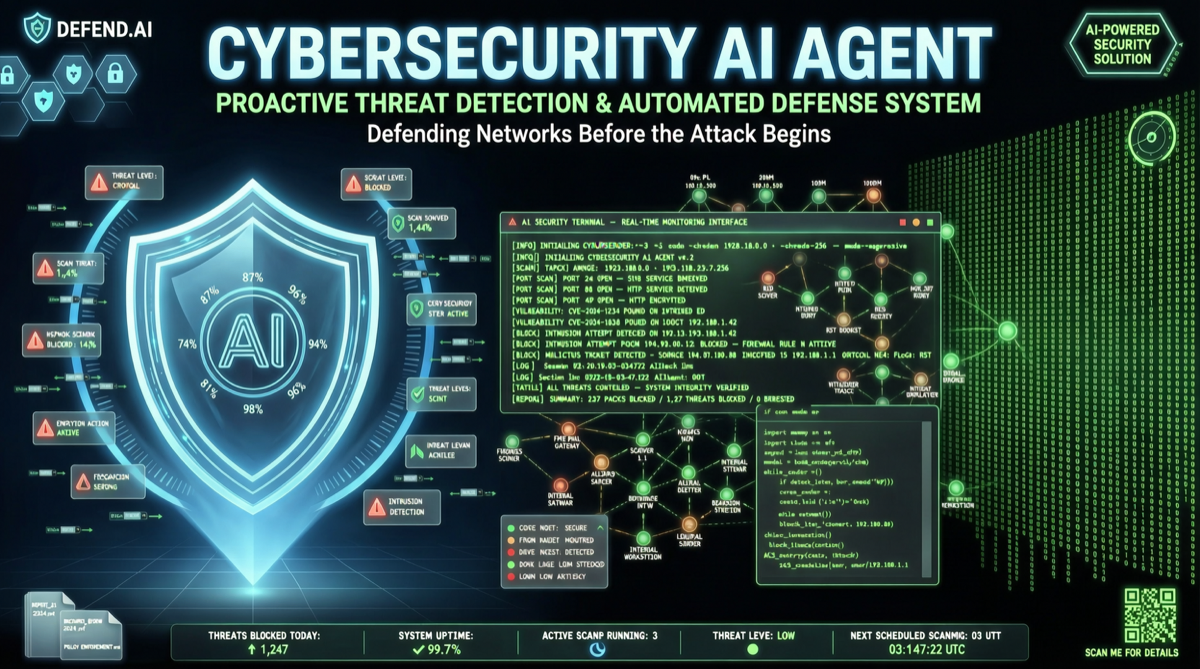
| Interface | Hacker-style terminal TUI |
| Workflow | Analyze → select tool → execute → interpret → adjust strategy |
How ReAct Mode Works
Thought: Target has port 443 open, should check SSL certificate configuration first
Action: ssl_checker --target example.com
Observation: Certificate expired 30 days ago, uses TLS 1.0
Thought: TLS 1.0 has known vulnerabilities, need to test cipher suites further
Action: nmap --script ssl-enum-ciphers -p 443 example.com
...The agent doesn’t blindly execute preset scripts — it dynamically decides the next action based on each step’s observations. This is nearly identical to how human security experts work.
Comparison with Similar Solutions
| Solution | Tool Integration | Autonomous Decision | Real-time Interaction | Open Source |
|---|---|---|---|---|
| CyberSentry | 8 real tools | ✅ ReAct dynamic decisions | ✅ TUI real-time output | ✅ |
| Burp Suite + AI Plugin | Depends on Burp ecosystem | Partial (advisory mode) | ✅ | ❌ |
| Traditional Script Chaining | Requires manual writing | ❌ Fixed workflow | Partial | Depends on script |
| Pure LLM Suggestions | ❌ No tool calling | ✅ Text-only suggestions | ❌ | ❌ |
Applicable Scenarios
Best suited for:
- Initial asset reconnaissance and vulnerability scanning for security teams
- Automated pre-reconnaissance for red team exercises
- Developer self-testing for security (pre-deployment checks for SSL, CORS, Headers, and other common configuration issues)
Not recommended for:
- Production-grade penetration testing requiring deep vulnerability discovery
- Formal security assessments involving legal compliance (AI decision traceability remains controversial)
Risk Warning
⚠️ For authorized security testing only. CyberSentry’s autonomous execution capability means it can perform extensive probing on targets without human supervision. Unauthorized use may violate computer security laws.
Quick Start
# Clone the repository
git clone https://github.com/example/cybersentry.git
cd cybersentry
# Configure NVIDIA NIM API Key
export NIM_API_KEY="your-key-here"
# Launch
python main.py --target example.comThe project uses a “hacker-style” terminal interface that displays the agent’s reasoning process, tool calls, and result analysis in real time during execution — perfect for learning and demonstration purposes.